
PFCLObfuscate - Protect Your PL/SQL
PFCLObfuscate allows you to protect the PL/SQL in your database without relying on Oracle's wrap.exe program. This is a very flexible and powerful tool that can be used to protect the Intellectual Property (IPR) in the actual PL/SQL. Sometimes the value or secrets are the code itself and our product can be used to protect this code. PFCLObfuscate allows you to remove the meaning from PL/SQL, yet it is still completely valid PL/SQL. This makes it much harder for someone gaining access to your database to read and understand your code.
Here is the PFCLObfuscate main interface:
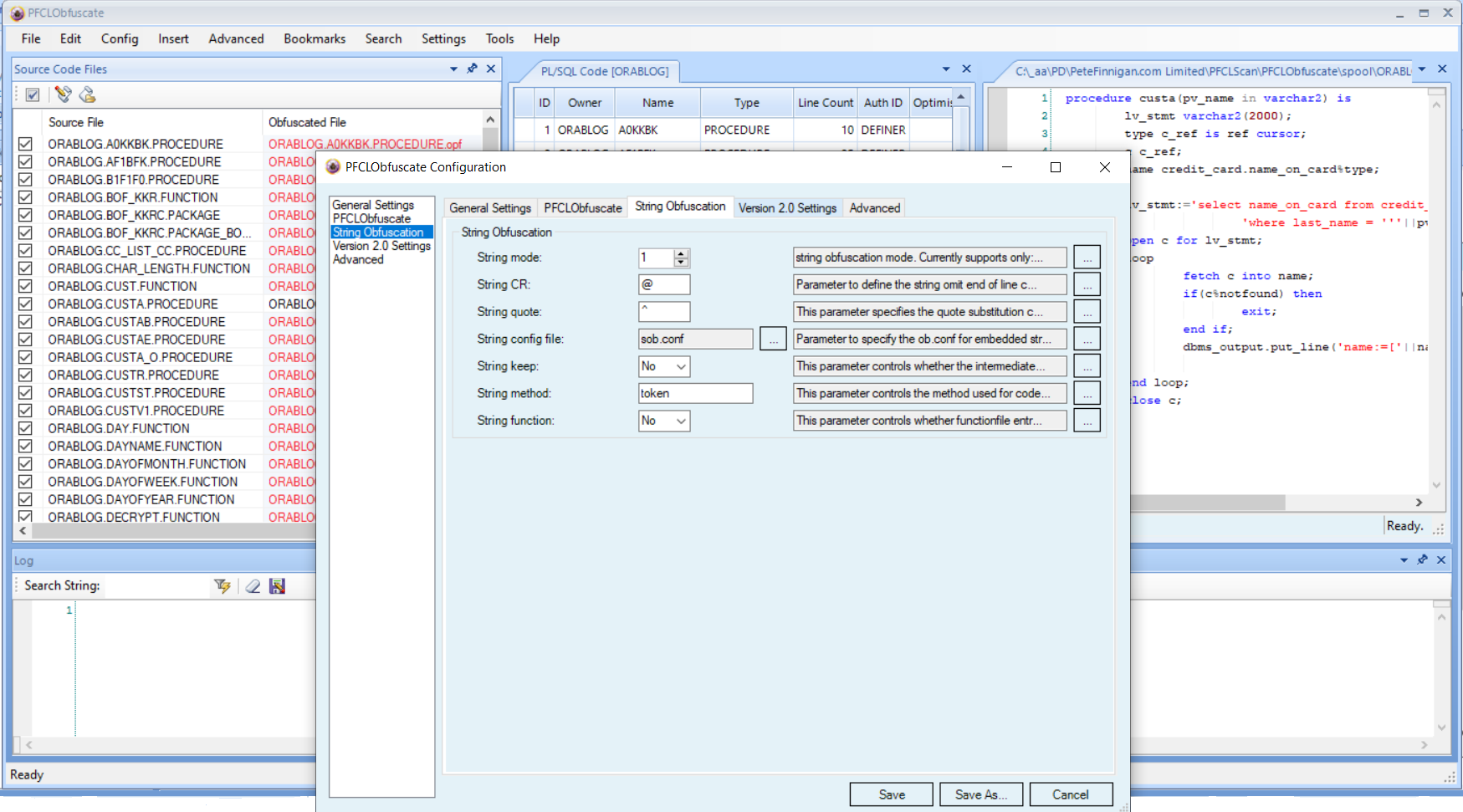
PFCLObfuscate also allows you to add license type features to your PL/SQL. This means that you can enable a license file that specifies such things as start dates and end dates to control how long and where your customers or employees can run your PL/SQL code. This licensing is added automatically to your PL/SQL code.
This is a Windows based software and it can be used by a developer to protect PL/SQL source code already deployed to a database. It needs to connect to a development or test database or even production to analyse the PL/SQL source code to be protected.
This product can also be run as a command line tool on a Windows PC. Because of this feature as a command line it can easily be integrated into other existing build programs and processes. PFCLObfuscate is licensed per installation of PFCLObfuscate and there are no fees or royalties for the protected PL/SQL.
What is PFCLObfuscate?
PFCLObfuscate as a toolkit is used to secure PL/SQL code. The idea of obfuscation is to make it hard for someone to steal the Intellectual Property held in your database source code written in PL/SQL.
Obfuscation is intended to remove the meaning from the source code without removing the functionality. So your code becomes hard to read and understand but still works in exactly the same way as before.
If you are really serious about protecting your IPR in your PL/SQL code then you also have to consider that once its deployed to a database anyone with permissions can read the source code from the database so you may also want to explore ideas to prevent your code from running in a different database if it is stolen or even prevent it from running in the database it is installed in in any other circumstance than was intended; i.e. maybe your code is run from a web form so running directly in SQL*Plus is not as intended.
If protections are added to your code to stop it from running when it should not then it also makes sense to protect the license code with tamperproofing code. These layers of protection when obfuscated can be wrapped with Oracles wrap program and the final result made safe from unwrapping.
We can provide the best protection of the IPR invested in your PL/SQL code.
Download PFCLObfuscate brochure
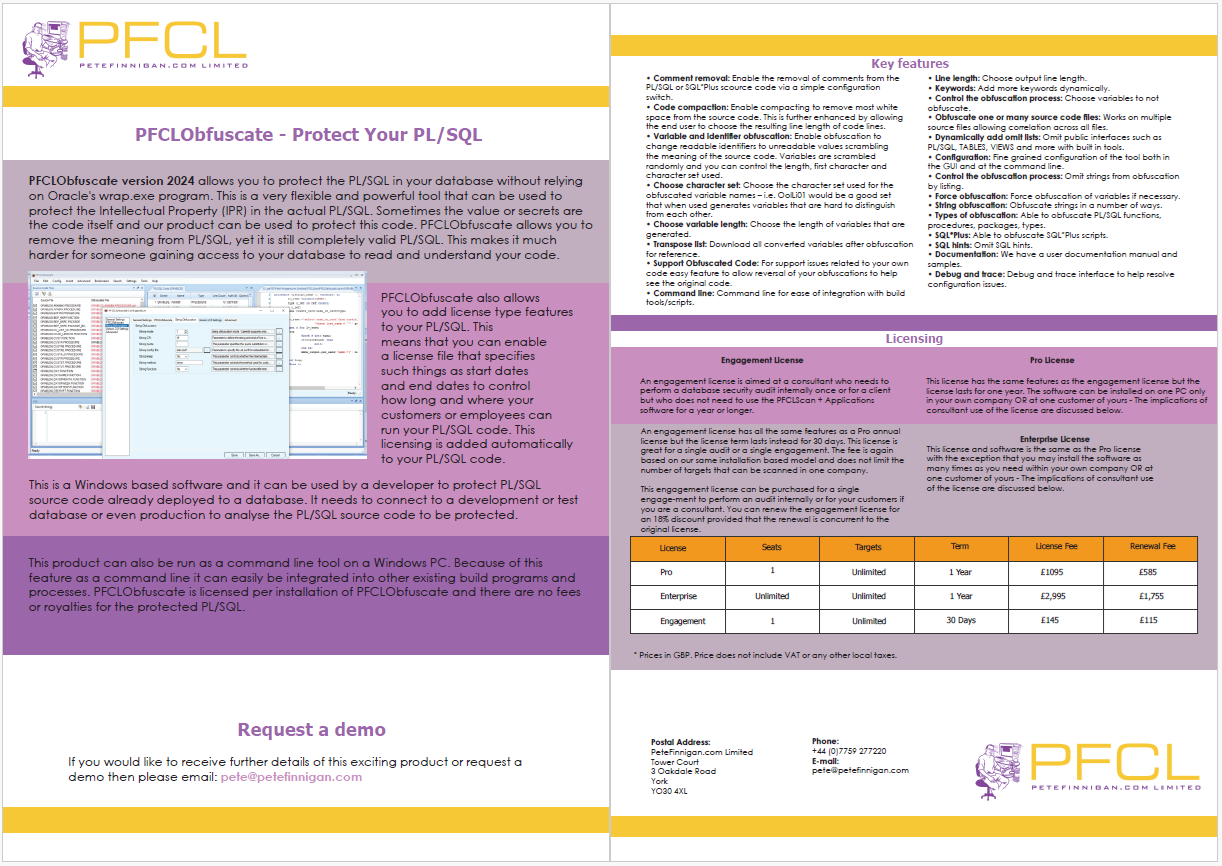
Click on the image below to download a PDF version of this brochure.
Learn More About PFCLObfuscate
- PFCLObfuscate Features
-
Learn more about the great features available in PFCLObfuscate
- Purchase PFCLObfuscate Licenses
-
Find out about all of our license types and their prices
- Ask PeteFinnigan.com Limited to Secure your Code
-
PeteFinnigan.com Limited are able to help you secure your own PL/SQL by offering setup and initial use of PFCLObfuscate as a service
- Find a Reseller
-
Find out about all of our license types and their prices
- PFCLObfuscate Articles
-
Read some articles about PFCLObfuscate
- PFCLObfuscate Blog
-
Read some Blogs about PFCLObfuscate
- PFCLObfuscate RoadMap
-
Find out more details of the roadmap for the PFCLObfuscate product
- PFCLObfuscate Home
-
The PFCLObfuscate Home page shows high level details of PFCLObfuscate and provides access to all of the other product details
Like to Purchase, More Details?, Want To Partner?
Please email pete@petefinnigan.com to enquire about the product; PFCLObfuscate can also be used as part of a consulting engagement with PeteFinnigan.com Limited where we can help you secure your PL/SQL for you as part of an engagement. Alternately you can purchase a license for PFCLObfuscate from us. Please email for details.
















